 CoroNet - a New Tool to Detect Fake Wi-Fi Networks
CoroNet - a New Tool to Detect Fake Wi-Fi Networks
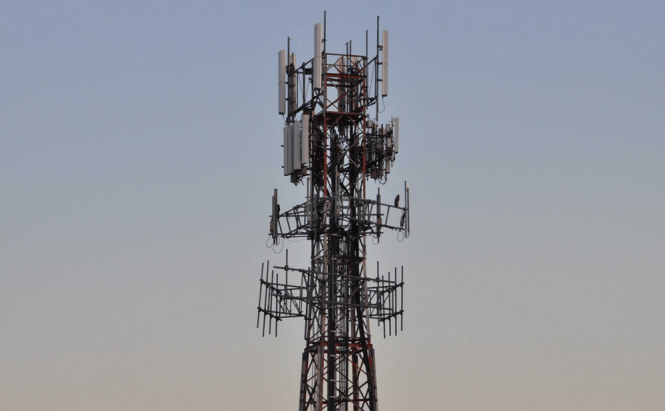
I'm not sure if you've heard about it or not, but last fall there was a lot of talk about U.S. surveillance agencies using fake cell towers to collect data about citizens and track their movements. Being totally honest, I originally thought that this was an exaggeration based on an isolated incident, but when the FBI's director admitted to using these so-called Stingrays, I had to believe it. Unfortunately, a similar concept can be easily applied for wireless Wi-Fi points. Basically the attacker would require a station which emits a stronger signal than the legitimate one, thus tricking devices into connecting through it instead of the regular server.
Up until now such things were considered highly improbable, as only governments would have the resources to pull off something like that (and we all know that governments never do such things). However, recent technology allows a savvy hacker to set something like this up for $350 while someone who isn't very technically skilled will need to pay $1.500 which let's be honest is not incredibly expensive. And since you can use such a trick to obtain valuable data from companies, it's not that even that far-fetched. Oh, I didn't tell you, the person (organization) that sets up the fake Wi-Fi access point will be able to track its users' exact locations, intercept data and listen in on their calls, so they can do some damage.
Fortunately, an Israeli company has developed a possible solution for this kind of problems. The application called CoroNet works on laptops, Android and iOS devices and is now being tested by to major European telephony carriers. From what I understood, the tool works by identifying several clues which are typically found in commjacking techniques. Although its developers are pretty secretive about the exact technique, they said that among other clues, the tool can identify the pattern of radio waves in a certain location which are specific to a hacker attack.



