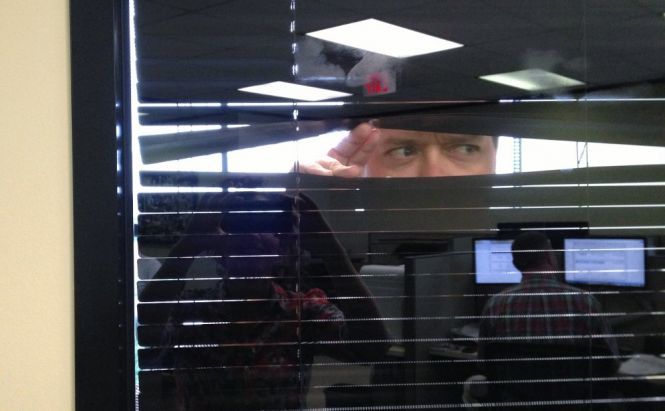
 Big Boss is Watching You, or Spying at Work
Big Boss is Watching You, or Spying at Work
Let's be honest: we cannot sit still all the day doing our work. From time to time we divert our attention from that things we are paid money for to check social networks or entertaining web pages. I am not speaking about those who even manage to play games, do shopping and so on (hopefully, those who read this article, are honest and responsible people for no to do that). In most cases all this is absolutely harmless for the productivity rates, because we all need a short break from time to time. Still, it is easy to understand those bosses who worry about their employees wasting time. Here comes the reason to install some spying software to monitor their computer activities. Moreover, there can be another weighty argument in favor of tapping into employees' computers: all these seemingly innocent activities can lead to the leak of some internal company's information.
Nowadays it is quite usual for organizations to control their workers' computers or corporate smartphones. Some of them may announce it from the very beginning, others don't find it necessary to notify that they keep watch over you. Prices for the so-called Internet surveillance programs start from a couple dozen dollars, and this is more than affordable for a self-respecting organization.
How can employers spy on you?
In this article I will dwell only on computer surveillance methods, but you should bear in mind that eavesdropping on phone calls or webcam monitoring of the office can also occur. So, as for computer surveillance, employers may check the web pages you use (are there any suspicious word combinations in your search queries in Google, or whether you book any flight tickets, or, heaven forbid, watch something inappropriate when other colleagues are out); which e-mails you send (if they cover your work topics or you just sort out your private life problems) and, say, which information you share on social networks. Speaking in a more professional way, all these can be performed through three main methods: desktop monitoring, log files exploring and packet sniffing.
The first method is probably the easiest and the most popular one. It is enough to install a special software that will replicate what you see at the moment on your display, by capturing screenshots of your desktop every specified period of time. Moreover, some desktop recording applications are able to act as keyloggers by recording every key you press and then sending this information to system administrators. Here I must mention that this type of software can be used not only by employers with good intentions, but also by malefactors to steal your personal information, for example, your logins and passwords.
The second method is based on exploring the files that your activity leaves in the system. You may erase all the e-mails from the Inbox and Sent folders, log out from your third-party accounts, still, some traces are always left. I mean, for example, web browsers cache or applications backup acting as the black box of an airplane, that can be accessed if something suspicious occurs. The administrator can look through these files remotely if hard drives of the company are interconnected, or just when the employee is absent.
The third method, packet sniffing, or packet analyzing, is originally used for performing diagnosis and troubleshooting of networks, but recently it became popular for activity monitoring tool. The information is transmitted over a network in the form of packets of about 1000-1500 bytes of data. The idea behind sniffing is logging the traffic passing over a network by capturing every packet and sometimes even decoding its data. If the sniffer is running on a computer within the corporate network, then it is possible to extract information about the pages you visit and what you look at there, what you download or stream.
Is it legal?
Of course, the answer depends on the country where you live and on the company itself. Common sense dictates that it is inappropriate to look after people so fixedly; however, in most cases there are not many restrictions. Most laws only ask employers to tell workers that they are being watched. In general, the rule that if the company owns the computer, then it has the right to access everything inside it, usually works. Speaking about the USA, according to the Electronic Communications Privacy Act, it is not illegal to access the stored electronic communication which implies monitoring of e-mails stored on servers. Also, in some states companies are even allowed to demand social media account information to increase the level of control. In some countries the policy is more loyal: for example, in Britain the Internet surveillance cannot be carried out without getting your consent. So, before arguing about the violating your rights, it's better to check the corresponding laws of your country.
How to prevent yourself from being caught?
First, do not try to find the source of spying and deactivate it. It is quite obvious, that sooner or later the administrator will detect the computer that is not responding and will fix the issue in no time. If the rules are strict and you cannot survive till the evening without checking Facebook feed and YouTube subscriptions, do it from your smartphone, tablet, or buy yourself a laptop.
If your network use is being constantly logged, the way to overcome it is to get off this network; fortunately, today it is possible due to the era of 3G and 4G services. Use a USB dongle / wireless tethering device / smartphone to establish mobile broadband connection. Of course, it will cost you money, so again it's up to you to decide whether it is really reasonable.
Anyway, remember the general rule: if you don't know if you are being monitored, act as you are. Caution will never bring you in trouble.



